Cloud Infrastructure: From First Principles To Practical Choices
.png)
Introduction
Most teams do not want to build data centers anymore, but they still need reliable, secure, and cost-aware infrastructure. Cloud infrastructure solves this by offering on-demand capabilities with standardized service and deployment models, and by shifting operations toward automation and governance. The sections below distill vendor-neutral guidance from NIST, ISO, CSA, CNCF, and the FinOps Foundation, with practical checklists and trade-offs you can apply today.
What Is Cloud Infrastructure
Cloud infrastructure is commonly defined by five essential characteristics, three service models, and four deployment models. The characteristics include on-demand self-service, broad network access, resource pooling, rapid elasticity, and measured service. Service models include IaaS, PaaS, and SaaS, while deployment models include public, private, community, and hybrid cloud.
NIST’s (National Institute of Standards and Technology) reference architecture also names core actors such as the cloud consumer, provider, broker, auditor, and carrier, clarifying boundaries and responsibilities in real systems.
Why it matters. These models provide a common language for design, governance, and contracts across providers and tooling.
Core Building Blocks (Compute, Storage, Network, Identity, Observability)
- Compute. Virtual machines, containers, and functions are the main units. Containers improve portability but introduce new image and runtime risks addressed in NIST SP 800-190.
- Storage. Block for databases, object for durability and analytics, file for shared POSIX workloads. Select redundancy, encryption, and lifecycle rules that align with SLA and compliance targets.
- Network. Software-defined networking enables segmentation, private connectivity, and policy routing across accounts and regions. Hybrid connectivity extends controls on-prem while honoring zero trust principles.
- Identity. Identity and access management (IAM) is the real perimeter. Map human and workload identities, enforce least privilege, and monitor entitlements. In complex estates, CIEM tools and processes help detect over-permissioned access and rightsize privileges.
- Observability. Metrics, logs, traces, and events drive reliability. CNCF guidance emphasizes instrumenting cloud-native platforms and workloads to maintain performance and availability.
Cloud Infrastructure Management (operations, automation, governance)

Good management blends SRE-style operations with service management rigor. Use policy as code for guardrails, automation for provisioning and remediation, and SLAs for expectations. ISO/IEC 19086 provides a common SLA lexicon and a metrics model for specifying measurable promises like availability and response time.
For security configuration hygiene, align with the CSA Cloud Controls Matrix and supporting auditing guidelines, and map to CIS Controls where helpful.
Cost is a first-class operational concern. The FinOps Framework treats cloud cost as a shared responsibility across engineering, finance, and product, emphasizing timely data, accountability, and unit economics.
Lifecycle hooks to automate.
Provisioning, identity bootstrap, baseline hardening, secrets, backup, vulnerability scans, drift detection, SLO monitoring, cost allocation, and decommissioning. Tie each hook to tickets or alerts with clear owners and success criteria.
Cloud Infrastructure Security (threats, controls, shared responsibility)
The shared responsibility model splits provider and customer duties, but customers still own identity, data, and configuration risk. Start with least privilege, network segmentation, encryption, vulnerability management, workload isolation, and continuous monitoring.
- Zero Trust. NIST SP 800-207 recommends shifting away from implicit trust based on network location to continuous verification and policy-based access at request time.
- Cloud control frameworks. CSA CCM v4 maps cloud controls across domains and offers implementation and auditing guidance.
- Workload security. NIST SP 800-190 details threats and mitigations for container images, orchestrators, and runtime, including signed artifacts and least privilege runtimes.
- Privacy in public cloud. ISO/IEC 27018:2025 provides guidance for protecting PII when the provider acts as a processor, complementing your ISMS controls.
Hybrid Cloud Infrastructure (patterns, trade-offs, providers)
Hybrid integrates on-premises and cloud resources as one system. It is useful for data residency, latency-sensitive workloads, or staged modernization. NIST recognizes hybrid as a deployment model that combines two or more distinct infrastructures with portability and orchestration.
Trade-offs.
- Pros. Control over locality, burst capacity, gradual migration, and risk isolation.
- Cons. Duplicated controls, more complex identity and network policies, and higher operations overhead.
- Good practices. Establish a consistent identity plane, standardize images and IaC modules, and define one change control path for both sides with common SLAs and metrics.
Monitoring And Reliability (practical checklists)
Define service level indicators for availability, latency, error rate, and saturation, then set SLOs tied to user impact. ISO/IEC 19086-2 provides a model for specifying SLA metrics, which you can adapt for internal SLOs.
Checklist.
- Instrument metrics, logs, and traces for every service and dependency.
- Track golden signals per service, including upstream and downstream calls.
- Alert on symptoms users feel, not just resource thresholds.
- Record releases, config changes, and incidents as first-class telemetry.
- Review error budgets in weekly ops and product forums to guide release pace.
Quick Checklist
- Architecture. Pick service and deployment models that fit regulatory and latency needs.
- Identity. Centralize IAM, enforce MFA and conditional access, review entitlements monthly, and adopt CIEM practices for high-scale estates.
- Network. Default deny, segment by environment and data sensitivity, and prefer private connectivity for critical paths.
- Data. Encrypt in transit and at rest, classify data, and apply retention and lifecycle policies.
- Workloads. Use signed images, minimal base images, and runtime restrictions.
- Observability. Emit metrics, logs, and traces with consistent labels across teams.
- Cost. Tag workloads, allocate shared costs, and review unit costs with product teams monthly.
- Compliance. Map controls to CSA CCM and your ISMS, and audit regularly.
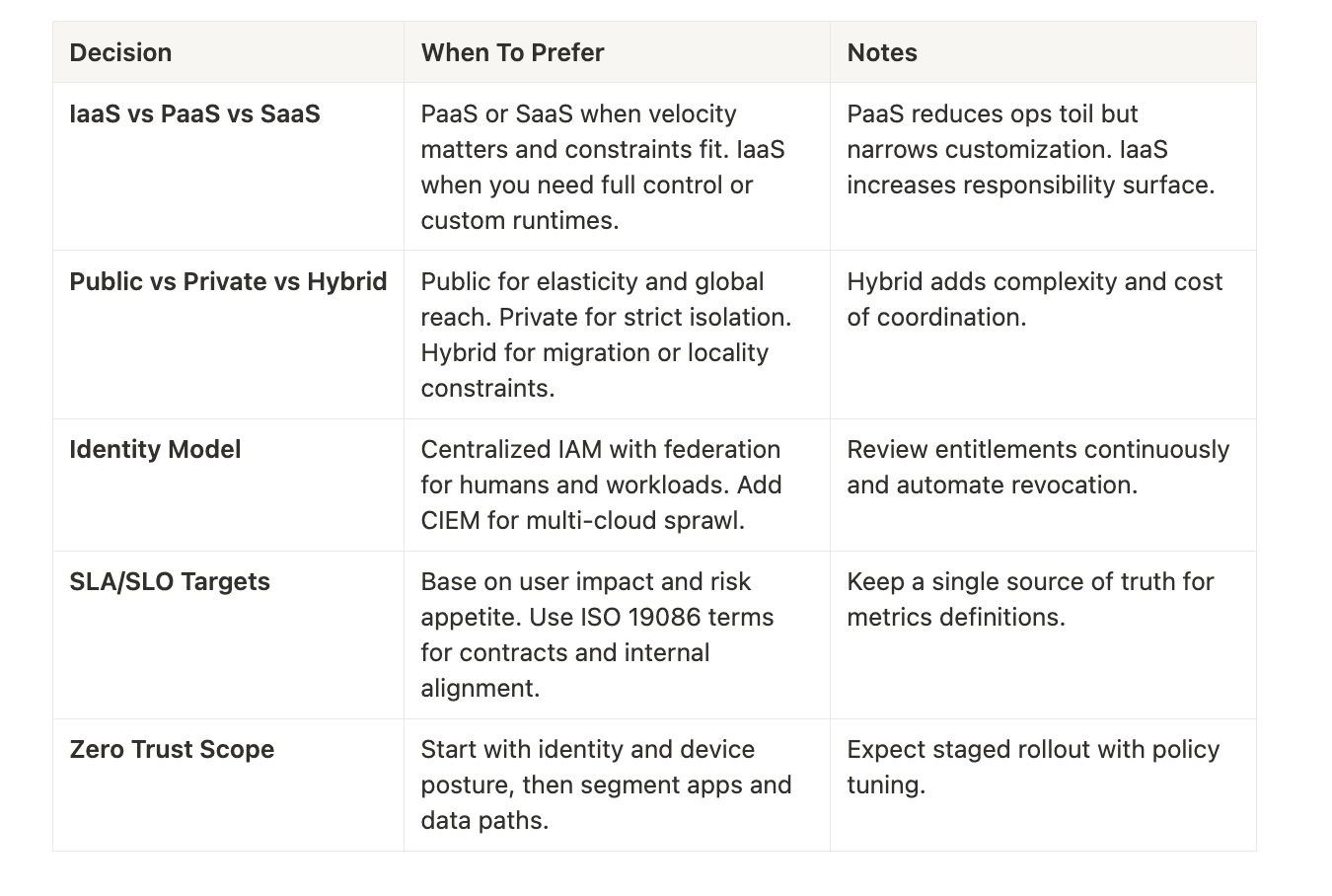
Decision Guide
Conclusion
Cloud infrastructure is not a tool set, it is an operating model built on shared definitions, measurable promises, disciplined security, and continuous observability. The models and controls from NIST, ISO/IEC, CSA, CNCF, and FinOps give you a neutral backbone you can apply across providers. Start with identity and SLAs, instrument everything, automate guardrails and cost allocation, and iterate with SLOs and error budgets. The result is secure, reliable, and economically sensible infrastructure that scales with your business.
FAQ
- Q: What is hybrid cloud infrastructure in practice.
- A: It is a composition of two or more distinct infrastructures with portability and orchestration across them, used for migration, locality, or risk isolation.
- Q: How do we express reliability targets.
- A: Use ISO/IEC 19086 SLA concepts and a metrics model to define clear terms and measures, then translate them into internal SLOs.
- Q: Where do we start with security controls.
- A: Map requirements to CSA CCM v4, adopt zero trust principles, and harden container supply chains per NIST SP 800-190.
- Q: How does CIEM relate to IAM.
- A: CIEM augments IAM by analyzing and correcting cloud entitlements to enforce least privilege across accounts and services.
- Q: How should we manage cost without slowing delivery.
- A: Follow the FinOps Framework to make cost a shared, data-driven practice with clear accountability and unit metrics tied to business value.



